Effective Strategies for eCommerce Fraud Prevention: Protect Your Online Store
Today's e-commerce businesses should secure their platforms and protect their clients from any e-commerce fraud that might happen. The emergence of clever cybercriminals who persistently exploit flaws in online transactions poses a constant threat to both businesses and customers.
You can learn more in this article about what eCommerce organizations should know about the different types of e-commerce fraud and the various methods and technologies available to identify and prevent fraud.
Discover effective eCommerce fraud prevention strategies to protect your online store. Safeguard your customers' information and transactions with proven techniques. Learn how to detect, prevent, and respond to fraudulent activities to ensure a secure shopping experience for your customers.
Read on!
Table of Contents:
- What Is eCommerce Fraud Prevention?
- What Are eCommerce Fraud Types?
- 5 Ways To Prevent eCommerce Fraud
What Is eCommerce Fraud?
eCommerce fraud is any deception or fraudulent behavior that occurs during online transactions, generally involving the theft of financial or personal information, unauthorized purchases, or misleading promises about items and services. It typically targets online shops, payment systems, and customers, leading to financial losses, reputational damage, and customer trust erosion.
Stolen credit card information, identity theft, account takeovers, chargebacks, and other forms of eCommerce fraud exist. Fraudulent transactions can result in financial losses for enterprises, reputational damage, and consumer inconvenience. As a result, comprehensive fraud prevention measures must be implemented in order to maintain a secure and trustworthy online environment.
What Are eCommerce Fraud Types?
eCommerce fraud can happen in a lot of ways. Here's a rundown of the most common types:
1- Identity Theft Image source: ecommercegermany
Image source: ecommercegermany
When someone steals your personal information, such as your Social Security number, bank account number, or credit card information, this is referred to as identity theft. Identity theft can be perpetrated in a variety of ways. Some identity thieves rummage through garbage cans in search of bank accounts and credit card statements.
Accessing company databases to obtain lists of client information is a more high-tech way. Once identity thieves have obtained the information they seek, they can destroy a person's credit rating as well as the standing of other personal information.
Identity thieves are increasingly relying on computer technology to gain personal information from others in order to commit identity fraud. They may scan the hard drives of stolen or discarded computers, hack into computers or computer networks, access computer-based public documents, or utilize information-gathering techniques to uncover such information.
2- Credit Card Fraud
eCommerce fraud encompasses any fraudulent conduct intended to abuse online stores. The most prevalent assaults include fraudulent purchases using stolen credit card details. eCommerce fraud, on the other hand, is increasingly taking the shape of account takeover or refund fraud, among other tactics. Fraudulent actors gain credit card information in a variety of ways and use it to conduct unauthorized transactions, resulting in financial losses for cardholders and businesses.
3- Chargeback Fraud
Chargeback fraud is a rising issue that affects all types and sizes of businesses. Chargebacks can occur for a variety of reasons, including corporate faults or customer dissatisfaction with a product or service.
Customers, on the other hand, use chargebacks to avoid returning things and requesting refunds, while fraudulent actors use them to steal from firms. In both circumstances, the negative effects of chargebacks can be devastating to a company's financial health and reputation.
4- Phishing and social engineering
Phishing attacks employ email or malicious websites to obtain personal information by impersonating a reputable organization. For example, an attacker may send an email that appears to be from a respected credit card business or financial institution, requesting account information and frequently implying that there is a problem. Attackers can acquire access to accounts when users react with the desired information. An attacker employs human contact (social skills) in a social engineering attack to gather or breach information about an organization or its computer systems.
An attacker may appear unassuming and reputable, claiming to be a new employee, repair worker, or researcher and even providing credentials to back up their claim. He or she may, nevertheless, be able to piece together enough knowledge to enter an organization's network by asking questions.
If an attacker cannot obtain sufficient information from a single source, he or she may contact another source within the same organization and depend on the information obtained from the first source to increase his or her credibility.
5- Account takeover fraud
Account takeover fraud ATO occurs when a cybercriminal acquires access to the victim's login credentials in order to steal money or information. Fraudsters use a variety of ways to break into a financial bank account and take control of it, including phishing, malware, and man-in-the-middle assaults, among others. Due to the financial damages and mitigating measures required, ATO is a major danger to financial institutions and their clients.
Existing accounts, such as a bank, credit card, and e-commerce, might be taken over by fraudsters. Some account takeovers start with fraudsters stealing personal information from data breaches or buying it on the Dark Web.
6- Counterfeit or Fake Products

Sellers offer low-quality or counterfeit goods masquerading as genuine goods, fooling customers and harming brand reputation. Counterfeit goods are imitations of genuine, legitimate products that were produced without the brand owner's permission.
Counterfeit items may appear visually identical to genuine ones, but they are frequently produced from different, low-quality materials. Counterfeit goods are unauthorized, copycat items that include the trademark(s) of the brand owner in an attempt to fool consumers into believing they are purchasing genuine products.
5 Ways To Prevent eCommerce Fraud
eCommerce fraud prevention is critical for the safety and credibility of your online business. Here are five practical methods for preventing eCommerce fraud:
1- Implement Secure Payment Systems
Make sure your eCommerce platform uses secure payment gateways that adhere to industry standards like the Payment Card Industry Data Security Standard (PCI DSS). By encrypting the data during transmission, this helps protect critical consumer information such as credit card numbers. This will help your customers trust your brand more.
2- Use Multi-Factor Authentication (MFA)
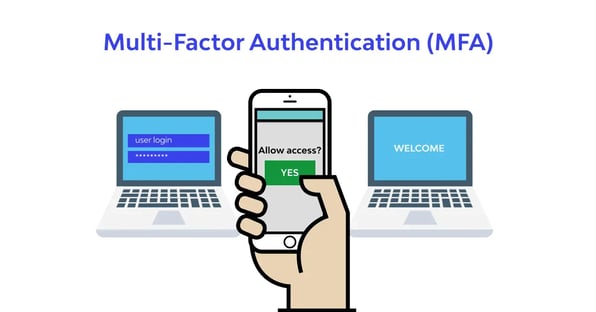 Image source: wallarm.com
Image source: wallarm.com
Multi-factor authentication adds an extra degree of security by asking consumers to submit other authentication factors, such as a unique code sent to their mobile device, in addition to their login and password, which adds an extra layer of security. Even if login credentials are compromised, this helps prevent unauthorized access.
3- Use Address Verification Systems (AVS)
AVS verifies the customer's billing address during checkout to the address on file with the credit card company. If there is a discrepancy, it could be a sign of possible fraud. Implementing AVS can aid in the detection and prevention of fraudulent transactions.
4- Suspicious Activity Should Be Monitored
Use fraud detection tools and regularly monitor transactions for any suspicious patterns or abnormalities. Multiple orders from the same IP address, unusually big orders, or a significant amount of transactions in a short period are all red flags. Automated systems and artificial intelligence-powered fraud detection solutions can assist in identifying suspected fraudulent actions.
5- Use Geolocation and IP tracking
IP tracking and geolocation are ways to establish the geographic position of an internet-connected device based on its IP (internet protocol) address. These strategies are frequently used in the prevention and detection of e-commerce fraud because they assist organizations in identifying odd or suspicious activities that may signal fraudulent transactions or unauthorized access.
Incorporating IP tracking and geolocation into fraud prevention and detection strategies strengthens e-commerce businesses' security measures, lowers the risk of fraudulent activities, and improves overall customer experience—all while assisting businesses in complying with local regulations while offering a more personalized user experience based on the customer's location.
